Brands hardly ever think of mapping APIs as a security surface until something goes wrong. A store pin moves. A service area disappears. Pickup points stop matching the back end. A location page still loads, but the directions are wrong and the customer blames the company, not the API. That is why mapping api protection deserves the same attention as any public-facing application layer. Google’s own Maps Platform security guidance is fairly direct on this point: teams should restrict keys, separate usage by application, review usage patterns, and avoid leaving production credentials wider than they need to be.
That security layer also matters on the business side. For multi-location companies, the mapping stack touches discovery, store accuracy, and local visibility at the same time. If a brand manages listings, pages, and location data through the Getpin local seo platform, map integrity becomes part of customer trust rather than a narrow engineering concern. In that setting, api key security, geolocation api security, and the effort to prevent unauthorized api changes all sit very close to revenue, support costs, and brand consistency. Google’s recommendations around key restrictions and usage reviews fit naturally into that broader operating model.

Where Unauthorized Changes Usually Begin
Security gaps rarely start with a loud alert. It is an old browser key with no strict referrer policy. A staging credential that survives into production. An internal endpoint that accepts more methods than it should. A token that proves identity but says too little about scope. By the time someone notices, the problem no longer looks like a configuration gap. It looks like data drift.
The patterns behind that drift are well documented. In the API Security Top 10 for 2023, broken object-level authorization, and unrestricted resource consumption remain familiar sources of damage. For map-driven systems, that can mean edits applied to the wrong location object, unauthorized reads across tenants or regions, or bursts of geocoding traffic that drain budget before the team even sees the spike. OWASP api security thinking becomes practical here: it gives teams a way to look at map endpoints as business-critical interfaces with real abuse paths.
A location stack is especially exposed because it tends to mix public and protected actions in the same ecosystem. The customer-facing map needs to be fast and simple. The internal tools for edits, store merges, delivery polygons, or branch metadata need tight control. When those boundaries blur, api endpoint hardening stops being a nice engineering phrase and turns into a production requirement.
Separate Read Traffic From Write Authority
A solid mapping setup treats reads and writes very differently. Public map rendering, basic lookups, and lightweight customer interactions can be scoped one way. Administrative actions, style management, location edits, and dataset changes need a much stricter path. REST tools for managing cloud maps, together with OAuth protocols, clearly define the security standard for critical server-side operations. Using OAuth2 for API mapping is most appropriate where data modification (on the write path) or privileged access is involved. This allows you to close vulnerabilities in places where regular API keys with broad privileges pose too great a risk for abuse.
This is also the point where a lot of teams get more value from identity rules than from network assumptions. In NIST SP 800-207 on Zero Trust Architecture, the focus shifts from network location to the resource itself. In plain terms, the request should be trusted because it proves who it is, what it can access, and whether that access still makes sense right now. That fits mapping systems very well. A service account that can update store geometry in one region should not be able to rewrite another region’s data just because it sits inside the same cloud project. That is the operational meaning of zero trust mapping apis.
Here is the request path many teams aim for once the system moves beyond a small prototype:
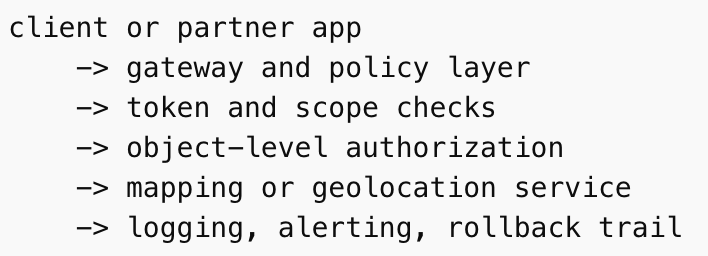
That middle section does most of the real work. It is where API gateway protection, JWT validation mapping, and BOLA prevention apis start carrying weight. The gateway screens methods, quotas, schemas, and origin patterns before traffic reaches expensive or sensitive services. Token checks confirm the caller and the audience. Object-level rules decide whether that caller is allowed to touch this exact store, map style, or service zone. OWASP’s current guidance is useful here because it keeps teams from confusing authentication with authorization. A valid token is not the same thing as permission to edit a location object.
The Small Controls That Save Teams Later
Security failures around maps often come from details that looked harmless during development. A wildcard origin in a hurry. Headers that were never tightened after launch. A certificate decision made once and forgotten. Those details deserve their own pass.

On the web side, CORS api configuration is often misunderstood. As MDN’s guide to CORS explains, browsers use CORS headers to decide which origins may read responses. That means broad origin allowances can quietly widen exposure in browser-based flows, especially when third-party scripts, dashboards, or partner integrations are involved. It also means secure api headers should be reviewed as part of the same surface, not as an unrelated checklist.
Transport settings deserve equal attention. And again, MDN’s explains about HSTS that the header tells browsers to use HTTPS for future connections and to upgrade insecure attempts automatically. For customer-facing location pages and embedded store tools, HTTPS api enforcement and HSTS mapping security help remove downgrade paths that attackers still look for when the surrounding stack is inconsistent.
Mobile clients add another layer of judgment. Android’s network security configuration documentation supports certificate pinning and cleartext traffic controls, so certificate pinning apis can make sense in apps that exchange sensitive mapping or location data over hostile networks. Still, pinning needs care. Done poorly, it can create avoidable outages during certificate rotation. Done properly, it narrows trust without turning maintenance into a trap.
| Control area | What it should do in a mapping stack |
| IP restrictions apis | Limit server-side calls to known origins or workloads where that model fits |
| rate limiting geolocation | Keep expensive endpoints from being abused or drained by sudden bursts |
| JWT validation mapping | Verify token issuer, audience, expiry, and scope before any sensitive action |
| CORS api configuration | Allow only the origins that genuinely need browser-based access |
| secure api headers | Narrow browser behavior and reduce accidental exposure |
| API gateway protection | Enforce quotas, schema checks, method rules, and visibility before the backend sees the request |
Watch For Drift, Not Just Attacks
One reason mapping abuse can sit unnoticed for too long is that it appears non-disruptive initially. The store locator still loads. The map tiles render. Requests keep flowing. What changes is the pattern. A regional account starts editing locations outside its scope. A client suddenly sends a larger share of requests to geocoding endpoints than it did last week. An old integration starts talking again after months of silence. This is where API traffic monitoring and geolocation insights catch what manual checks miss.
The safest teams look for mismatches between identity, geography, timing, and volume. They track who changed a map object, from where, through which token, and in what deployment window. They keep rollback paths for location datasets and style changes. They review cost spikes as security signals rather than billing annoyances. Google’s security guidance places real emphasis on checking API usage and reviewing restrictions already in production, and that habit matters more than many teams think because drift is often visible in usage long before it is visible to customers.
What Holds Up In Production
The most reliable protection is often the most straightforward. OAuth-backed server workflows for privileged operations. Narrow scopes. Object-level checks on every write. Sensible origin policy. Clean TLS enforcement. A gateway that blocks what should never reach the backend. Logging that tells the team what changed before customers do.
That stack will not make mapping APIs invisible. It will make them governable. And that is the real goal. Brands do not need a flashy security story around maps. They need stable location data, clean customer journeys, and a system that does not let one loose credential rewrite part of the brand’s public footprint. When those controls are in place, mapping api protection stops feeling like an isolated security exercise and starts looking like disciplined infrastructure management.