Implementing a working virtual environment involves intense knowledge of resource management and accurate command execution. This guide aims at providing a consistent digital base without compromising cost-effectiveness to the developers and small businesses. With a lightweight distribution chosen and background processes prioritized, users can deliver impressive performance without having to spend too much money.
By learning the command line interface, one is able to be more precise about every facet of the operating system. Managing a server is a complex task that requires the optimization of security measures and access in order to make the daily process run smoothly.
With proper planning and configurational strategies, any administrator could develop an efficient infrastructure that will expand in tandem with their increasing digital needs and initiatives.
Establishing the Initial Server Foundation
Choosing the correct operating system is the initial challenge towards establishing a cost effective environment with your applications. The Debian based distribution or Ubuntu Server, is usually favored by most administrators since it provides a rich community support base and low resource overhead.
As soon as the installation is made, users have to pay attention to securing the root access and creating a non-privileged user that would work on a daily basis. This will reduce the chances of unintentional damage to the systems when the high-level configurations are in progress.

Many providers offering affordable linux vps hosting provide pre-installed templates that simplify this entire setup phase significantly for beginners. By choosing a minimal install, you ensure that no unnecessary background services consume your valuable memory or processing power during peak usage times. Configuring the timezone and updating the local package repository are also essential steps to maintain synchronicity with global networks and security patches.
Maximizing Resource Efficiency and Speed
- Select a lightweight desktop environment if a graphical interface is absolutely required for tasks.
- Disable unused daemons to free up volatile memory for your primary web applications today.
- Use swap files to provide a safety net when physical RAM reaches its total capacity.
- Install monitoring tools to track CPU usage and identify processes that drain system energy.
- Optimize the disk input output operations by selecting the most appropriate file system for data.
- Compress log files regularly to prevent storage saturation on smaller virtual solid-state drives.
How Can Users Secure Their New Linux Environment?
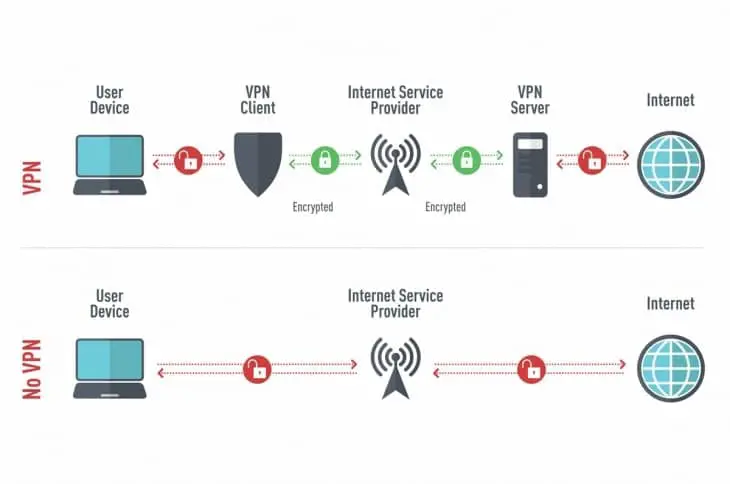
The issue of security must not be considered as a secondary consideration when constructing a cost-efficient server that is to be used in front-facing services. The best firewall tool that can be put in place to ensure that there will be no unauthorized connection attempt by third parties is a strong firewall.
Administrators must modify the default ports of communication so as to prevent automated brute force attacks in the standard ports of entry. The use of public key authentication as opposed to traditional passwords provides an added protection to the login procedure.
Efficient Software Installation and Management
- Utilize package managers to ensure all installed software remains current and secure from threats.
- Group related services into containers to isolate their dependencies and prevent versioning conflicts easily.
- Temporal directories are cleaned frequently to reclaim space and ensure high-speed file system performance.
- Repetitive configuration operations should be automated with shell scripts to minimize the possibility of human errors.
- Attach external drive volumes to store large files in the form of media to make the main partition neat.
Strategic Backup and Recovery Planning
- Have automated data copies to an off-site location to minimize business continuity in case of failure.
- Restore operations are often done on tests just to make sure that the backup files are in a condition that can be used.
- Have several copies of vital databases in order to restore the data that has been deleted or corrupted accidentally.
- Apply incremental backup to save space and speed up the duration needed for transfers.
- Before shifting sensitive archives to another storage provider, it is best to encrypt all the archives and then store it in a secondary storage provider.
Future Infrastructure Growth
Creating a strong digital foundation depends more on thoughtful software selection and robust security practices than on costly hardware. True efficiency comes from eliminating unnecessary components and concentrating on the core services that directly support your objectives. This approach allows for steady growth without placing excessive strain on your budget.
Choosing affordable Linux VPS hosting offers a practical balance between performance and cost for today’s creators. With a structured setup and ongoing maintenance, it is possible to operate a professional-level system that stays both responsive and dependable.
Frequently Asked Questions
Can I upgrade my resources later?
Most virtual providers allow you to scale your processor and memory as your traffic grows without reinstalling the system.
Why is key authentication better than passwords?
Cryptographic keys are nearly impossible to guess, providing much stronger protection against modern hacking techniques compared to text strings.